I ended up spending too many hours in demystifying how SharePoint online works in a federated environment but apparently I didn’t get many details, though I got few but it wasn’t in one location. I thought let me put all the information I collected here.
Let’s start with some basic; As we all know SharePoint online is a SAAS offering (Software As A Service) and for user to consume this service their account should be present somewhere for the system to authenticate them.
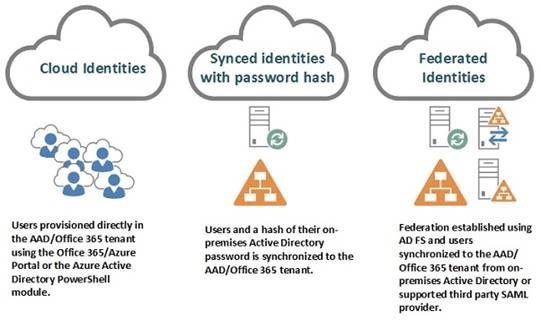
As of now we have got 3 identity models:
Let’s see in detail about each one of them at a very high level:
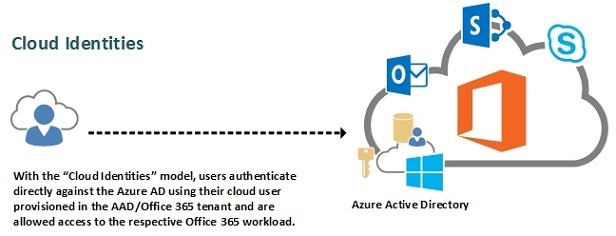
Cloud Identities:
To put it simple, these are the account which gets created in cloud.
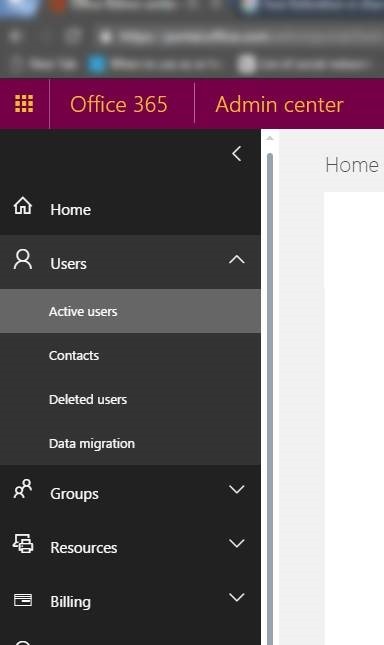
Go to https://portal.office.com/adminportal/home#/users
Click Users Tab in the left side navigation and select ACTIVE users in it
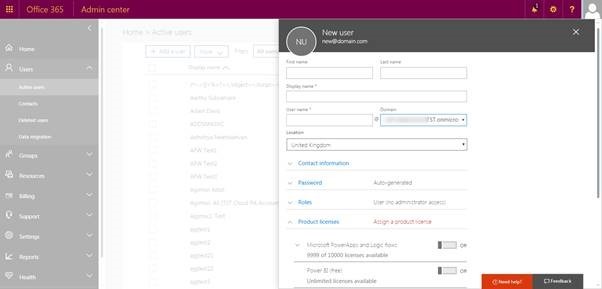
Click ADD user in the right side:
You will see the list of domain associated for your tenant under Domain Drop down and in that, one of domain would like something like this YOURTENANTNAME.Onmicrosoft.com
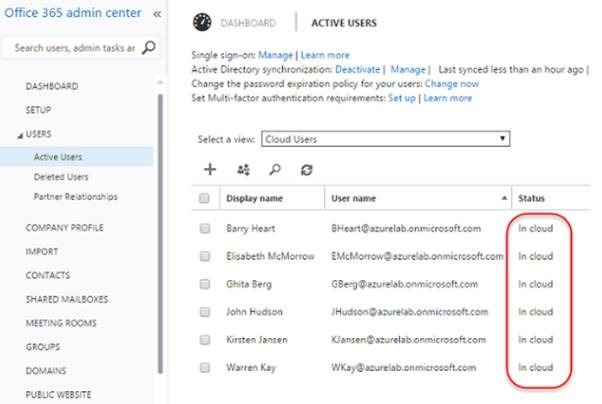
Create an account with this Domain been selected, eventually you will see that those users created with this domain will be showed as CLOUD account in the active user’s page
The major benefit of the cloud identity model is that you do not need to make any changes or deploy any new servers in the on-premises infrastructure.
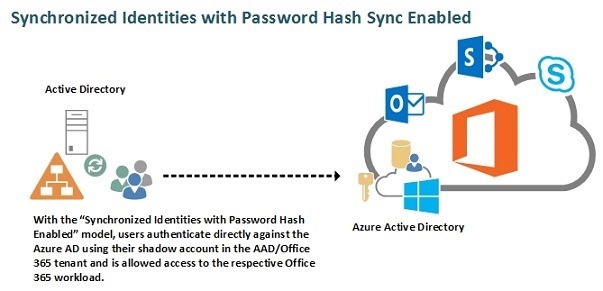
Synchronized Identities:
The second identity model is synchronized identities, where the existing users in the on-premises Active Directory are synchronized to the AAD/Office 365 tenant using a directory synchronization tool.
In this case any account created in on-prem would get synced with Office 365 and any account that syncs like this would look like this in ACTIVE users page.
The major benefit of using this identity model over the cloud identities is that users will be provisioned automatically using the directory synchronization tool and will be able to use the same set of credentials as they already use in their on-premises Active Directory resulting in not a “single sign-on” but “same sign-on” scenario where the user object and passwords are managed in the on-premises Active Directory. In a “same sign-on” scenario, the end user will, as mentioned, be able to use his existing credentials but needs to authenticate when accessing an Office 365 workload.
it’s important to note that the end user passwords will not be stored in the AAD/Office 365 tenant. It will be a hash of a hash of the on-premises Active Directory password that will be stored there and the password itself cannot be retrieved through the hash of the hash of the password by a malicious user.
Let’s talk more on Federation model and also on the modern authentication in the next blog post.


Leave a comment